By John Robert Morton, Student and Alumni Affairs Liaison, and Ashley Watts, APU Graduate
Environmental conservation is important, and quite a few of the University’s students and faculty member have dedicated their efforts toward protecting the environment.
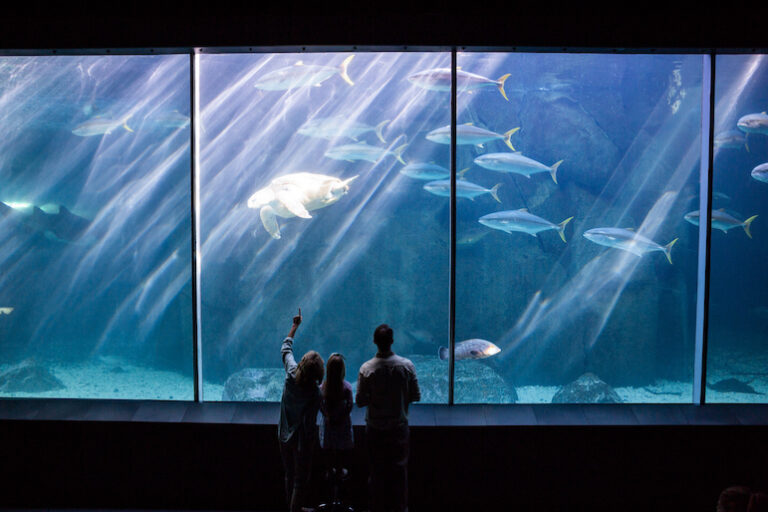
One of those conservationists is APU alumna Ashley Watts, whose work in conservation has created a better environment for aquatic animals and people in Michigan. As an animal welfare host and team lead for SEA LIFE in Lansing, Michigan, Ashley has helped to maintain a sustainable model for aquatic animals.
Developing a Love for Nature and Conservation

As a child, Ashley spent a significant amount of time exploring the waters of Michigan with her family. Traveling on her grandparents’ houseboat, they sailed to many different ports around the eastern side of Michigan and often traveled to Ohio and Canada as well. Her trips enabled Ashley to develop a love of the water and aquatic animals.
Finding the Right Academic Path
Ashley graduated with a bachelor’s degree in psychology from Adrian College in Adrian, Michigan. However, she never quite found her niche in the psychology field.
While taking classes for her psychology degree, she worked as an accountant. This experience was useful because it made her comfortable speaking in front of people and discussing topics like grants and food budgets.
Later, Ashley got a job at a petting farm. From that experience, Ashley realized that her true love was working with animals.
Ashley began research to see how she could get a degree geared toward working with animals and wildlife. She needed a school that would allow her to work full-time, but found that most schools required in-person attendance and were exceptionally expensive.
Ashley began looking for an alternative educational experience and came across American Public University (APU). After reviewing different academic programs, she chose the bachelor’s degree in natural sciences.
“I stumbled across a description of the bachelor’s degree in natural sciences, and I have not regretted it for a single day!,” Ashley says.
Creating a Professional Path in Aquatic Conservation
While taking classes for her bachelor’s degree in natural sciences, Ashley took a job as an events intern at the Potter Park Zoo in Lansing. She says, “The team was amazing, and the zookeepers were always happy to share insight and conservation efforts. The zoo even has a program where keepers will stand at a designated spot, talk about the importance of a given animal and answer any questions.”
After Ashley’s internship ended, the zoo kept her on as a part-time employee doing odd jobs for events throughout the rest of the year. She later heard about a job as an animal welfare host at an aquarium called SEA LIFE Michigan and applied.
Ashley was quickly offered the job and was promoted to the Team Lead position within two weeks. She loves talking to guests about the importance of each animal, and SEA LIFE does amazing conservation work.
After many months, a husbandry position opened on the Aquarist team, and Ashley was highly encouraged to apply. She now handles many parts of the aquarium and is involved with many conservation efforts.
Some of the conservation efforts that Ashley is involved in include:
- Local cleanups
- Seahorses, stingray, and sea star breeding
- Turtle and tortoise rescues
- Aquarium behavior studies for confined animals
Advice to Future Students
Ashley’s professional progression has been anything but straight and steady. However, she notes that her previous jobs gave her useful skills and knowledge.
“There is no one ‘right’ way to be in the field of conservation,” observes Ashley. “Every professional I have spoken to or worked with has a different educational and career background. Keep your education broad so you can make your studies specific. Have a focus but be open to options you had never even thought of trying before.”
About the Author
John Robert Morton is a Student and Alumni Affairs Liaison and has been with the University for 14 years. His bachelor’s degree in European history is from Troy University in Troy, Alabama. He also completed master’s degrees in political science and sports management from American Military University. As a liaison, John Robert enjoys helping students and alumni to achieve their personal and professional goals.
About Our Department
The AMU and APU Alumni Affairs Office is dedicated to sustaining lifelong relationships with university alumni by providing engaging opportunities to stay involved and connected. We work closely with a variety of stakeholders to strengthen the alumni experience and to offer a variety of benefits, services, activities, and events throughout the year.
As a team, the Alumni Affairs team works to build and sustain relationships with alumni along their personal and professional journeys. We actively look for ways to recognize and showcase alumni, telling their stories to motivate and encourage students in the pursuit of their goals.
If you are a member of the alumni community and are looking for ways to remain actively involved, please contact alumni@apus.edu and speak with a member of the team.