Guarding your personal cybersecurity and protecting yourself from cybercrime should be important to anyone who uses electronic devices. Cybercrime Magazine forecasts that by the year 2025, cybercrime will cost $10.5 trillion globally, up from $3 trillion in 2015. According to Cybercrime Magazine, cybercrimes involve:
- The deliberate destruction of data
- Stolen money
- Theft of personal and banking information
- Theft of intellectual property
How Do Cyber Attacks Occur?
To prevent yourself from becoming a cybercrime victim, it is essential to understand how cyber attacks occur and what you can do to avoid them. According to CompTIA, 95% of cybersecurity breaches occur due to human error.
One of the most common cyber attacks involves a hacker introducing malware to your computer or smartphone. The malware can get onto your computer or smartphone if you click on a link in an email or text message or you visit a fake website that closely mimics a legitimate site.
Often, users get malware on their electronic devices without even knowing it. As a result, their personal information can be leaked or sold, or they experience a malfunction with services on their computer or smartphone.
In addition, hackers can flood a network or server with more requests than it can process, which is known as a distributed denial of service (DDOS) attack. The network or server can’t function properly, which can be irritating for personal users and costly for business users.
RELATED: LiFi: A Better Way to Ensure Cybersecurity on Computers
Phishing
Another common cyber attack involves phishing. According to Simpilearn, phishing is a prominent type of cyber attack where a hacker impersonates a trusted source through a fake email. When a user clicks on a link in the fake email, a virus is downloaded to the user’s smartphone or home computer, and the hacker can gain access to confidential information or personal account credentials.
Such emails can appear highly legitimate at first glance. The email may include a company logo and a supervisor’s name, and it may be worded in a way that is very similar to past communications. An unsuspecting employee may open the link thinking that it came from a supervisor or colleague, and once the virus downloads itself, the hacker may access sensitive information that can cause substantial harm to a company.
Hackers may impersonate a state government, a federal agency, a social media site or a retailer. These emails are commonly designed to cause the user to panic and act without thinking; they may threaten the closure of an account or some other problem that needs quick resolution.
To avoid becoming a victim of phishing, never open email attachments that cannot be verified as legitimate. If there is any question whether an attachment is legitimate, call the email’s sender to verify it, especially if you’re not expecting an email from that sender.
It’s also helpful to carefully review the content of a suspect email. Phishing emails often contain misspellings and grammar mistakes; also, their web addresses and email addresses may slightly vary from the legitimate sources.
Other Ways Hackers Invade Your Personal Cybersecurity
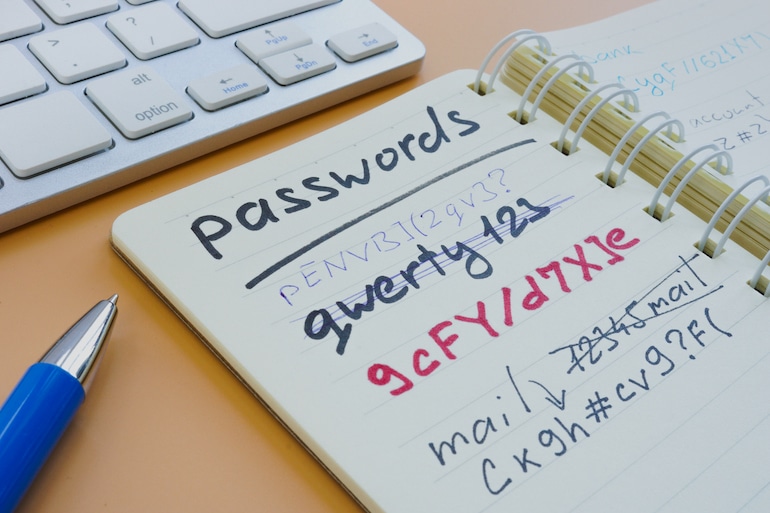
There are additional ways hackers try to invate your personal cybersecurity. For instance, hackers often try to determine your passwords, especially if those passwords are simple ones such as “1234” or “password.” Ideally, create complicated passwords that include various letters, numbers, and characters, and don’t use the same password for several sites.
Public Wi-Fi can also result in a cyber attack. Unsecured Wi-Fi connections are an easy way for hackers to gain access to any personal information transmitted over Wi-Fi.
If you must use public Wi-Fi, install a virtual private network (VPN). Using a VPN provides secure end-to-end encryption and may be available through your virus protection provider.
In addition, keep your antivirus software up to date. In addition to protecting computers and tables from viruses, antivirus software from Norton or McAfee can conduct scans of devices, remove cookies, and clear trackers that make your device vulnerable.
RELATED: How to Maintain Your Cybersecurity as You’re Traveling
Common Sense and Education Are Key to Maintaining Your Personal Cybersecurity
Overall, using common sense can be beneficial in maintaining your personal cybersecurity. Take the time to create multiple passwords for different websites, don’t use passwords that are easy for hackers to guess and check emails carefully. Also, take the time to study new cybersecurity breaches reported in the news and learn lessons from them.

Comments are closed.